133 private links
The other day I read 20 most significant programming languages in history, a “preposterous table I just made up.” He certainly got preposterous right: he lists Go as “most significant” but not ALGOL, Smalltalk, or ML. He also leaves off Pascal because it’s “mostly dead”. Preposterous! That defeats the whole point of what “significant in history” means.
So let’s talk about some “mostly dead” languages and why they matter so much.
Finally it's here!! :-)
Probably the feature that I was missing more since I started using Telegram!!!
It deserves a mention here :-)
Ever considered setting up and running your very own git server? It’s actually
quite easy! In this post, I’ll outline the steps I took to set up my
own so that you can give it a try yourself. But first, why
might you even want to go through the trouble of setting up your own server?
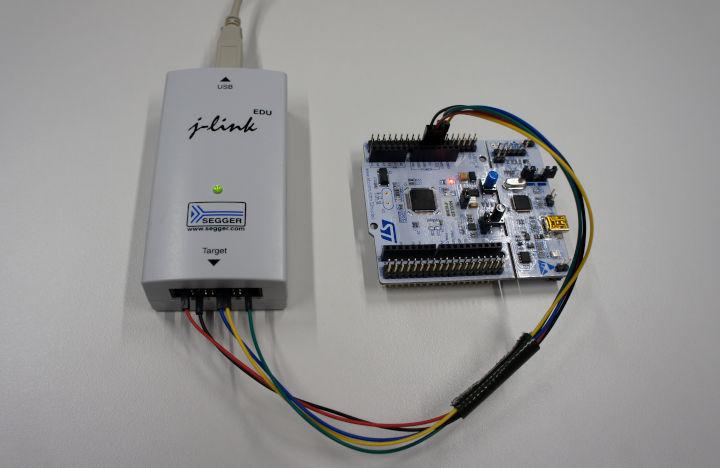
The firmware of microcontrollers usually contains valuable data such as intellectual property and, in some cases, even cryptographic material.
Stop Using Markdown For Documentation
I developed these programming exercises while working at 1010data. Each summer we’d put a batch of half a dozen or so interns through a week-long intensive K training program, including this set of puzzles, and then set them loose on the real codebase.
These problems vary in difficulty from trivial to moderately difficult (in non-escalating order), and are suitable for beginners or anyone wishing to brush a little rust off. A solution is provided for each problem in k3- click and hold on the gray area beneath each IO sample to reveal it. Most problems have at least one elegant solution, but many have multiple valid approaches- see how many ways you can satisfy the requirements!
Atbswp is a new graphical utility (Python3) that can be used to record the mouse and keyboard events, and reproduce (play) them identically as many times as you want by either clicking a button or saving it as a script and running it without having to relay on Atbswp.
VoLoc, a system that uses the microphone array on Alexa, as well as room echoes of the human voice, to infer the user location inside the home.

After the first case of covid-19, the disease caused by the new strain of coronavirus, was announced in the United States, reports of further infections trickled in slowly. Two months later, that trickle has turned into a steady current.
Timo Zimmermann about software engineering, leading teams, consulting and start ups.
This guide explains how to edit remote files with Vim on Linux. Starting from Vim 7.x version, the netrw plugin allows you to edit remote system files.
Why on earth would someone would pick C to start a new project in 2020? Surely there is a newer language with more shiny features that’s better right? Well I can’t speak for other people but I’ll tell you my reasons.
First of all let me preface this by saying that of course this is a biased opinion and the language I pick for something depends on the context it’s going to be used in. For example; I doubt I’ll ever be reaching for C when writing a web service simply because the ecosystem around that domain isn’t great and I’m not itching to write my http framework at this time.
But for games, more specifically cross-platform games C is a clear winner for me because it provides me with exactly the things I’m looking for which is reliability, simplicity and performance.
Like many developers, I have been interested in Rust for quite some time. Not only because it appears in so many headlines on Hacker News, or because of the novel approach the language takes to safety and performance, but also because people seem to talk about it with a particular sense of love and admiration. On top of that, Rust is of particular interest to me because it shares some of the same goals and features of my favorite go-to language: Swift. Since I've recently taken the time to do try out Rust in some small personal projects, I wanted to take a little time to document my impressions of the language, especially in how it compares to Swift.
The tradition of a "Hello, World" program goes back at least to 1978. But for modern coders, what's an appropriate "Hello, World"?
When polarizing topics are discussed in meetings, passions can run high and cloud our judgment. Learn how mental models can help you see clearly from this real-life scenario.
ffsend is a fully featured CLI client for Firefox Send. This article explains how to securely share files from commandline with ffsend on Linux.
Comparison among the number of command line options for various commands for v7 Unix (1979), slackware 3.1 (1996), ubuntu 12 (2015), and ubuntu 17 (2017).
The number of command line options has dramatically increased over time; they tend to have more options and there are no cases where programs have fewer options.
