132 private links
How to run an internet speed test from the Linux command line. We examine two tools that both use the speedtest.net service to test your connection speeds.
Watch out! If you start reading this paper you could be lost for hours following all the interesting links and ideas, and end up even more dissatisfied than you already are with the state of software today. You might also be inspired to help work towards a better future. I’m all in :).
This post overviews the paper Confident Learning: Estimating Uncertainty in Dataset Labels authored by Curtis G. Northcutt, Lu Jiang, and Isaac L. Chuang.
I like to use Makefiles. I like to use Makefiles in Java. I like to use Makefiles in Erlang. I like to use Makefiles in Elixir. And most recently, I like to use Makefiles in Ruby. I think you, too, would like to use Makefiles in your environment, and the engineering community would benefit if more of us used Makefiles, in general.
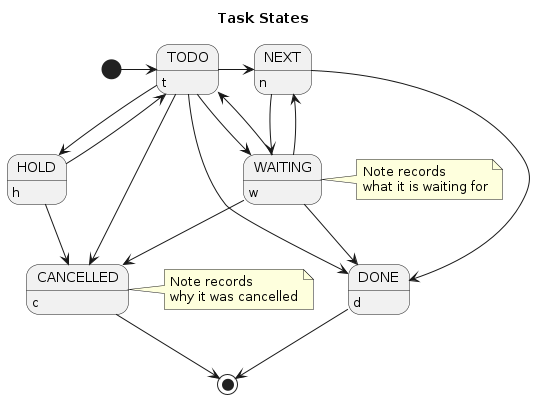
A comprehensive description of how I currently use org-mode.
I have always held that the act of programming is something that is done in an abstract realm and only later translated into a programming language. That programming should involve much more thinking than actual writing.
I mostly still stand by that but my years as a readability reviewer at Google raised my awareness of the fact that it takes time and practice to use a language well. Many were the hopeful C++ programmers who wrote fully functional and reasonably object-oriented code in Java but with a heavy C++ accent that couldn't quite meet the bar of elegance in Java (even if a C++ programmer might think it mostly elegant apart from the "flaws" of Java).
So how much does the choice of programmimg language matter? Is there or could there be a language that could be considered perfect?
This article discusses GPT-2 and BERT models, as well using knowledge distillation to create highly accurate models with fewer parameters than their teachers
A list
of things (not only) computer science students tend to
erroneously and at times surprisingly believe even
though they (probably) should know better.
A function to return the number of digits in an input (natural) number provides many learning opportunities for a new programmer
In this step-by-step tutorial, you'll learn how to build a mobile application with Python and the Kivy GUI framework. You'll discover how to develop an application that can run on your desktop as well as your phone. Then, you'll package your app for iOS, Android, Windows, and macOS.
Good software developers can't write code without help from the internet. It's incorrect to try to assess them in interviews by asking them to write down code from memory.
Learn how to use TF-IDF and scikit-learn to extract important keywords from documents. This is a full working example using the Stack Overflow dataset.
Commentary: The world rightly lauds Linus Torvalds for Linux, but Git will arguably have a bigger impact.
UPDATE: With respect to terminology, check out Drew Neil’s comment below. In Vim, I’ve been using splits for years. Splits are great: view 2 files at the same time view 2 parts of the s…
Learn some of the things you can create by checking out PySimpleGUI's demo folder. This gives you just a taste of what you can create using PySimpleGUI
This recent Tweet erupted a discussion about how logistic regression in Scikit-learn uses L2 penalization with a lambda of 1 as default options. If you don’t care about data science, this sou…
Learn how to use the k-means clustering algorithm to segment data.
What lessons can we learn from old code that becomes unkillable?
In this brief guide, we will discuss how to install 'motivate' and 'fortune' programs to display random quotes from commandline in Linux.
