133 private links
L1 Terminal Fault/Foreshadow explained in ~three minutes For a more detailed technical view of L1 Terminal Fault, please see this deeper dive with Jon Masters.
At the North America edition of the 2018
Linux Security Summit (LSS NA), which was held in late August in Vancouver,
Canada, Kees Cook gave a presentation on some of the dangers that come with
programs written in C. In particular, of course, the Linux kernel is
mostly written in C, which means that the security of our systems rests on
a somewhat dangerous foundation. But there are things that can be done to
help firm things up by "Making C Less Dangerous" as the title
of his talk suggested.
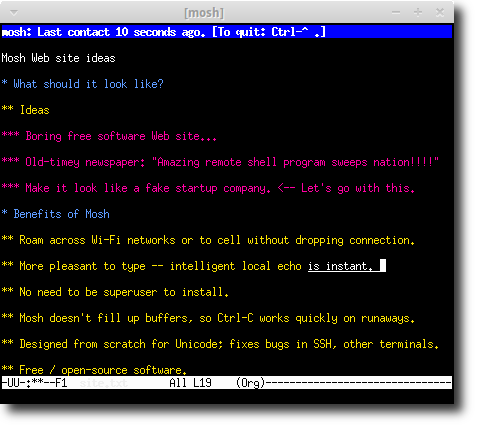
Mobile shell that supports roaming and intelligent local echo. Like SSH secure shell, but allows mobility and more responsive and robust.
10 Years Surveillance Systems and USB Cameras Designer
The Pentbox is a safety kit containing various tools for streamlining PenTest conducting a job easily. It is programmed in Ruby and oriented to GNU / Linux, with support for Windows, MacOS and ever…
This tutorial shows how to use eCryptfs to encrypt a directory on Ubuntu 16.04. eCryptfs is a POSIX-compliant enterprise-class stacked cryptographic f...
zbackup is a globally-deduplicating backup tool, based on the ideas found in rsync. Feed a large .tar into it, and it will store duplicate regions of it only once, then compress and optionally encrypt the result. Feed another .tar file, and it will also re-use any data found in any previous backups. This way only new changes are stored, and as long as the files are not very different, the amount of storage required is very low. Any of the backup files stored previously can be read back in full at any time. The program is format-agnostic, so you can feed virtually any files to it.
This is achieved by sliding a window with a rolling hash over the input at a byte granularity and checking whether the block in focus was ever met already. If a rolling hash matches, an additional full cryptographic hash is calculated to ensure the block is indeed the same. The deduplication happens then.
Anyone who has gone through the trouble of setting up a secure website knows what a hassle getting and maintaining a certificate can be. Let’s Encrypt automates away the pain and lets site operators turn on and manage HTTPS with simple commands.
No validation emails, no complicated configuration editing, no expired certificates breaking your website. And of course, because Let’s Encrypt provides certificates for free, no need to arrange payment.
In response to the Snowden revelation that the CIA compromised Apple developers' build process, thus enabling the government to insert backdoors at compile time without developers realizing, Debian, the world's largest free software project, has embarked on a campaign to to prevent just such attacks. Debian's solution? Reproducible builds.
Reproducible builds, as the name suggests, make it possible for others to reproduce the build process. "The idea is to get reasonable confidence that a given binary was indeed produced by the source," Lunar said. "We want anyone to be able to produce identical binaries from a given source."
If you're a web developer, you've probably had to make a user account system. The most important aspect of a user account system is how user passwords are protected. User account databases are hacked frequently, so you absolutely must do something to protect your users' passwords if your website is ever breached. The best way to protect passwords is to employ salted password hashing. This page will explain why it's done the way it is.
There are a lot of conflicting ideas and misconceptions on how to do password hashing properly, probably due to the abundance of misinformation on the web. Password hashing is one of those things that's so simple, but yet so many people get wrong. With this page, I hope to explain not only the correct way to do it, but why it should be done that way.
Through the years, I have settled on maintaining my sensitive data in plain-text files that I then encrypt asymmetrically.
