133 private links
Large neural networks have created interest in low-precision arithmetic, fitting more numbers in memory. But low-precision memory brings back old problems.
Most of us last saw calculus in school, but derivatives are a critical part of machine learning, particularly deep neural networks, which are trained by optimizing a loss function. This article is an attempt to explain all the matrix calculus you need in order to understand the training of deep neural networks. We assume no math knowledge beyond what you learned in calculus 1, and provide links to help you refresh the necessary math where needed.
PandaPy has the speed of NumPy and the usability of Pandas (10x to 50x faster).
If you round the result of every computation, then you can get exactly correct financial calculations using floating-point numbers, for realistic ranges of values.
Facebook AI has developed the first neural network that uses symbolic reasoning to solve advanced mathematics problems.
Nota is a nice terminal calculator with rich notation rendering. It is designed for your quick calculations and therefore provides you with a tiny and beautiful language so you can express your ideas easily. Nota is all about beauty and ASCII art.
Ryohei Hisano and Didier Sornette wrote in 2012 a paper titled, “On the distribution of time-to-proof of mathematical conjectures.”
Today Ken and I discuss predicting the end to mathematical conjectures. This is apart from considering odds on which way they will go, which we also talk about.
Nine years ago the Christmas issue of the New Scientist magazine analyzed a small set of solved mathematical conjectures and used it to forecast when the P vs. NP conjecture would be solved. The article estimated that the “probability for the P vs. NP problem to be solved by the year 2024 is roughly 50%”.
Mathematicians regard the Collatz conjecture as a quagmire and warn each other to stay away. But now Terence Tao has made more progress than anyone in decades.
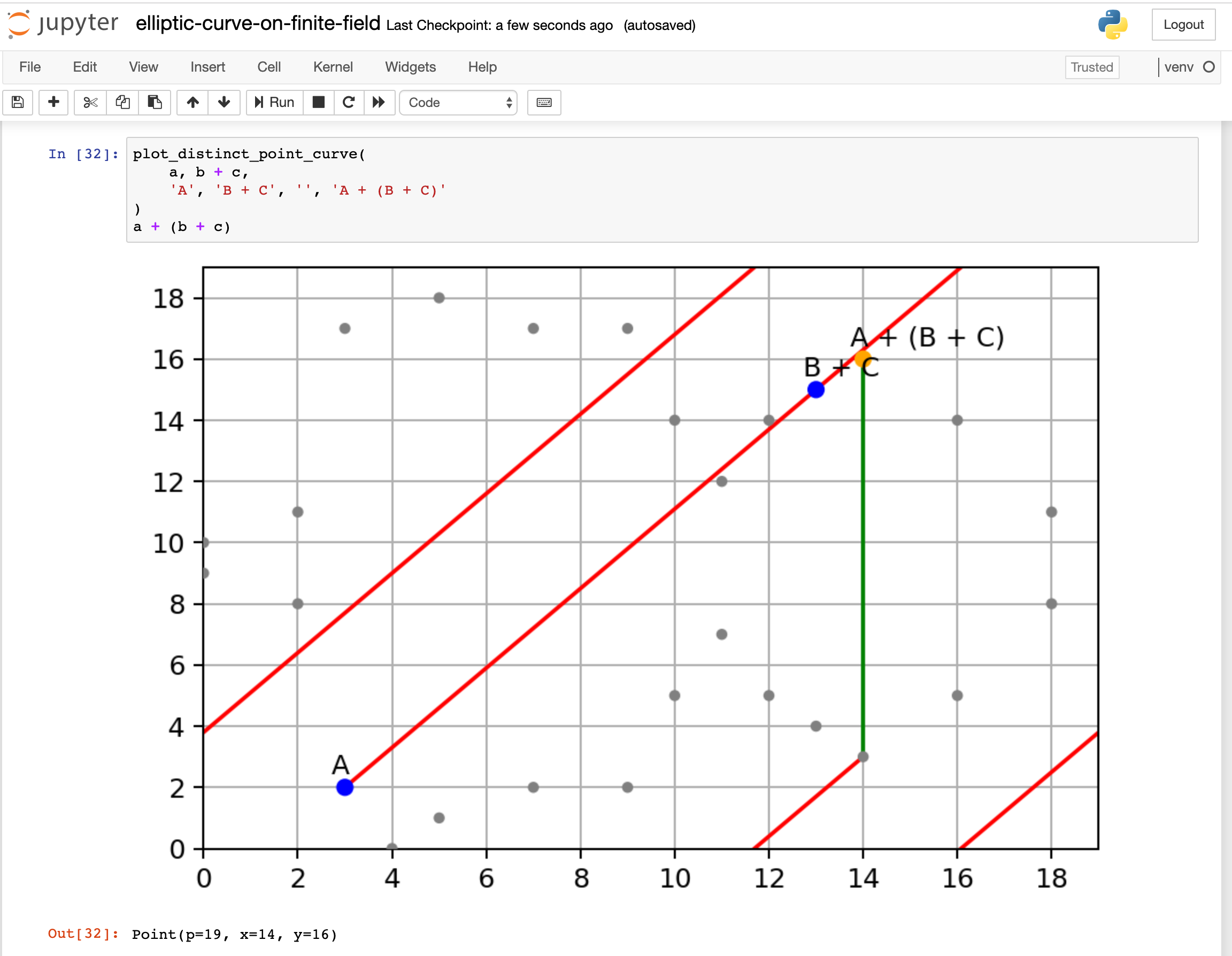
Recently, I am learning how Elliptic Curve Cryptography works. I searched around the internet, found so many articles and videos explaining it. Most of them are covering only a portion of it, some of them skip many critical steps how you get from here to there. In the end, I didn’t find an article that really explains it from end-to-end in an intuitive way.
With that in mind, I would like to write a post explaining Elliptic Curve Cryptography, cover from the basics to key exchange, encryption, and decryption.
Calculate digits of π. From scratch, that is, using only addition, subtraction, multiplication, and division.
Daniel J. Bernstein, Bo-Yin Yang. "Fast constant-time gcd computation and modular inversion."
elkai is a Python 3 library for solving travelling salesman problems without external dependencies, based on LKH by Keld Helsgaun.
You’ve probably played with model trains, for instance with something like the Brio set shown below.1 And if you’ve built a layout with a model train set, you may well have wondered: is it possible for my train to use all the parts of my track?

